25 Jun 2020 SmartZone Management Security – Part 1

SmartZone Management Security – Part 1
Whilst everyone is focusing on perimeter security such as Multi-Factor Authentication, Firewall’s and remote access technologies (Contact Purdicom for WatchGuard information) what about the other devices that sit on the LAN which aren’t protected by the firewall from users within?
Today we will be looking at the Ruckus SmartZone integrated with Active Directory / LDAP allowing you to delegate access based on Windows Security Groups, only letting users whom you wish to access the management plane to access it.
Step 1
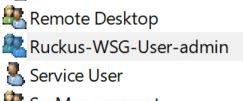
Create a Windows Security Group called “Ruckus-WSG-User-account name”, the account name must match a user that is defined on the SmartZone. Once you have done this just add members to that Security Group.
Here you can see the user we will map against is “admin” the default account of the SmartZone.
Step 2
Define the AAA server in Administration > Admins and Roles > AAA
Notice we do not use the “Default Role Mapping” feature as this would then allow all Active Directory users to access the management interface and all appear as the same user.
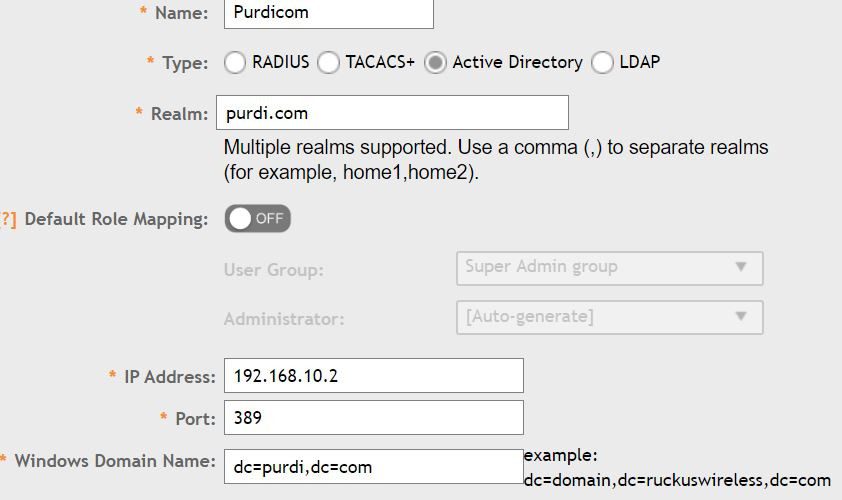
If you created a separate User account on the SmartZone ensure this is apart of a Group on the SmartZone.
Step 3
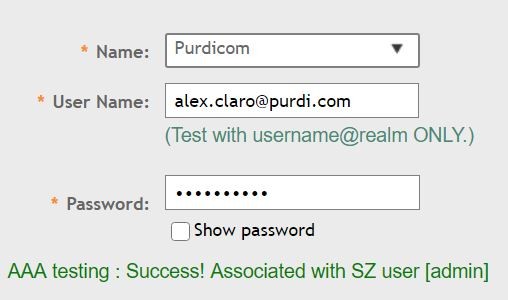
Now we have the AAA Server setup we can test! Click the “Test AAA” Button and ensure your account is associated with a user on the SmartZone.
Step 4
Login to the SmartZone with your Active Directory credentials and you will see in the top right your login name.
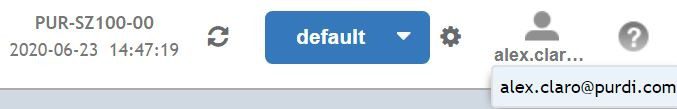
Its that simple you can ensure the main admin password for the SmartZone is hidden away whilst delegating access and creating custom roles without users needing to remember multiple passwords.
If you would like to get in touch with any further questions about this article or any other technical enquiry, please contact us on +44 (0) 1488 647 647
Author: Alex Claro – Solutions Architect Team Lead at Purdicom (CCNP, CWNA). To read this article and more by Alex on LinkedIn check here: https://www.linkedin.com/in/alex-claro/detail/recent-activity/posts/